IT-Grundschutz
The German IT Security Standard
The Security "Recipe"
Enabling companies to ensure information security at relatively low cost and effort is the objective of the German Federal Office for Information Security (BSI). Its IT-Grundschutz Catalogues and BSI standards constitute a framework for protecting information within the company.
Designed to serve as a security "recipe", the IT-Grundschutz Catalogues do not only describe occurrence probabilities, but also consider expected losses and implementation costs. A traditional and elaborate risk analysis is not required: Based on a modular principle, IT-Grundschutz defines risks for typical IT processes as well as appropriate countermeasures for you to implement.
To make the implementation of IT-Grundschutz a success, plan42 supports you throughout all phases:
1 Initiating the Security Process
First, we work with you to define requirements and objectives, which forms the basis for your security guideline.
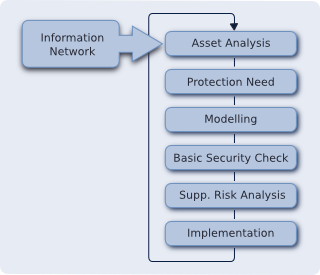
2 Analysing your IT Structure
Which is the scope for the implementation of IT-Grundschutz? After this question has been answered, we collect information about the relevant technology.
3 Determining Your Protection Requirements
Which level of protection is required for your information technology and related applications? Based on this question we select the appropriate measures to implement.
4 Modeling the Components
This step serves to model your IT network and components using the building blocks of the IT-Grundschutz Catalogues.
5 Performing a Basic Security Check
A gap analysis shows your current level of IT security and allows you to identify any security controls that need to be implemented. These controls are not limited to technical improvements: they also include organisational aspects, human resources, and the physical infrastructure of your organisation
6 Identifying Additional Measures
Are there any risks or highly vulnerable components that are not considered in the IT-Grundschutz Catalogues? Which additional measures do they require?
7 Implementing Your Strategy
We now help you prioritise and implement the outstanding actions. In this context, it is crucial to continuously monitor the implementation progress and results.
Certification & Other Checks
Successful implementation allows you to apply for an ISO 27001 certification on the basis of IT-Grundschutz. Besides, plan42 also offers audits and gap analyses to provide security assessments with varying scopes and for different stages of implementation to determine your company's IT-Grundschutz conformity.
And what can we do for you?
Would you like to learn more about our services? Please download our service description "ISO 27001 & IT-Grundschutz", or feel free to contact us.
